commentary Commentary
Commentary: The four deadly cybersecurity sins most of us are guilty of
Safeguarding your files and personal information on your smartphone or laptop from hackers is not rocket science, yet many negate to take basic pre-cautionary measures, says one cybersecurity expert.
File photo of a man using a laptop. (AFP/Thomas Samson)
SINGAPORE: Many people would have been advised by their IT departments, service providers or the Government to “use a strong password”, “protect your passwords” and “update your software regularly”, but have no idea why these are necessary cybersecurity measures.
It may be that “why” is usually not explained and if it was, explanations may have been very technical.
Such advice is also often ignored as these actions seem time-consuming yet ineffective.
But basic cybersecurity need not be rocket science. How you secure your smartphone or computer should be no different from how you secure your physical house.
You protect your assets in your home by preventing unsolicited and unauthorised access to your house. Similarly, protecting the personal information on your smartphone or computer requires restricting access to the data on it.
So why do many neglect to do so?
The main difference is that a house is visible whereas the digital world is not. Human nature makes us more protective of things we can see, so more effort is naturally exercised when it comes to the protection of our physical assets compared to our digital ones.
Where many have picked up bad cybersecurity habits, such lax, sloppy actions would not be conceivable in the context of securing our physical homes. There are four statements in particular that seem ridiculous in the latter context, and yet are surprisingly common sins in the realm of cybersecurity.
1. I AM USING A 3-DIGIT NUMERIC PADLOCK FOR MY FRONT DOOR
Imagine a door locked by a 3-digit numeric padlock. How secure can it be given that there are only 1,000 possible combinations between 000 and 999 inclusively?
If it takes a thief one second to try one combination, it will take 1,000 seconds or less than 17 minutes to open the lock.

In the digital world, the computational capabilities brought about by the advancement of computers and cloud computing mean that thousands or even millions of combinations can be attempted every second.
It is thus important to ensure that your password is of a sufficient length so that it will be more difficult for a hacker to succeed using similar “brute-force” attacks by running through all the possible permutations of your password.
2. THE COMBINATION FOR MY HOUSE DOOR IS 1234567890
Even if the password is of a sufficient length, the use of smart computer algorithms as well as artificial intelligence can also shorten the time for a hacker to crack a password.
These algorithms utilise dictionaries of commonly-used words, certain patterns of characters or numbers, or even personal data mined from the internet to make intelligent guesses of your passwords.
Simple but long passwords such as “MyNameIsStevenWong” take less than three days for a computer to crack, according to an online password analyser developed by a non-profit online community of cybersecurity experts.
There are many ways to create a secure and complex password.
One simple method is to use a phrase that you can remember and construct the password using the first character of every word while keeping any number or special character in the phrase.
To illustrate this, using the phrase “My name is Steven Wong and creating complex password can be simple in 2018!”, the password “MniSWaccpcbsi2018!” can be generated.

3. I HAVE PLACED THE KEY UNDER THE FLOOR MAT
Imagine you have installed the strongest lock to protect your house but have the habit of leaving the key under the floor mat of your front door for convenience sake. This will effectively render the lock useless and make your otherwise secured house vulnerable to theft.
Likewise, you may have created a very strong password but chose to write it on a piece of post-it and stick it onto your computer monitor or the back of your keyboard. How secure is that?
A common excuse is that there are too many passwords to remember and some company policies are for passwords to be changed every few months. Writing it down seems to be the easiest way to “store” passwords but this is also the easiest way for someone else to obtain your passwords.
It might be better to use a password manager to securely store all your passwords.
A password manager is like a secured key cabinet used to store the different keys in a building. You then need to ensure that the lock to the cabinet is strong.
Likewise, the login for your password manager needs to be secured by a strong password.
4. THERE IS A LARGE HOLE IN THE WALL AND I AM NOT FIXING IT.
If there is a large hole in the wall that enables an intruder to enter your house and bypass all the doors and locks, most people will immediately patch the wall up. However, when there are similar vulnerabilities in their smartphone apps or computer software, these don’t seem to be given as much urgency or priority.
This was evident in major cybersecurity incidents such as the WannaCry ransomware outbreak last year where over 200,000 computers around the world were compromised, resulting in billions of dollars in economic loss.
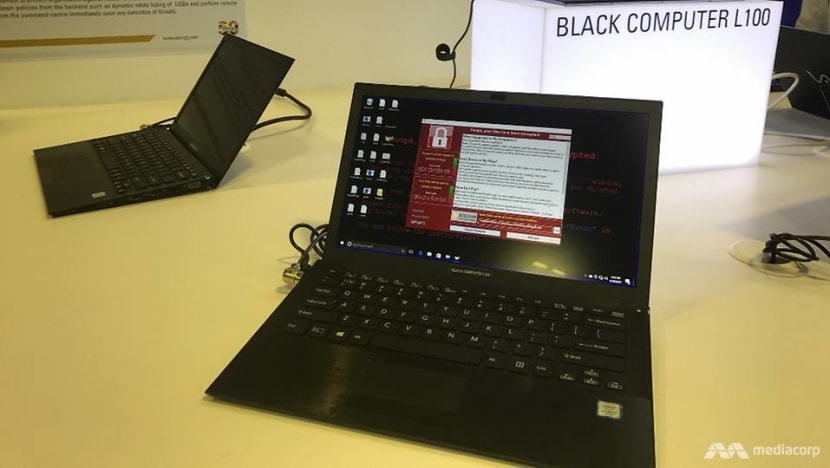
Unlike the patching of walls in your homes which can be expensive and may take a few days, the patching of bugs in your software and other fixes that may come with it is mostly free and takes at most a few minutes.
Most modern software also have automatic patching in-built so there is no good reason why your software should not be patched with the most recent update.
EASY TO IMPLEMENT
Basic cybersecurity is definitely not rocket science.
Unlike securing a house, the methods discussed are mostly free and easy to implement.
Given that 81 per cent of data breaches are caused by weak or stolen passwords according to the Verizon Data Breach Investigations Report in 2017, adhering to such simple cybersecurity practices will definitely go a long way towards better securing your assets in a digital world.
Dr Steven Wong Kai Juan is president of the Association of Information Security Professionals and programme director for the information security degree programme at the Singapore Institute of Technology.