commentary Commentary
Commentary: The SingHealth breach and the uphill task of governing cyberspace
Anonymity, long-distance penetration and the quality of stealth suggest a very different international order is at play in cyberspace, says one observer at the S Rajaratnam School of International Studies.
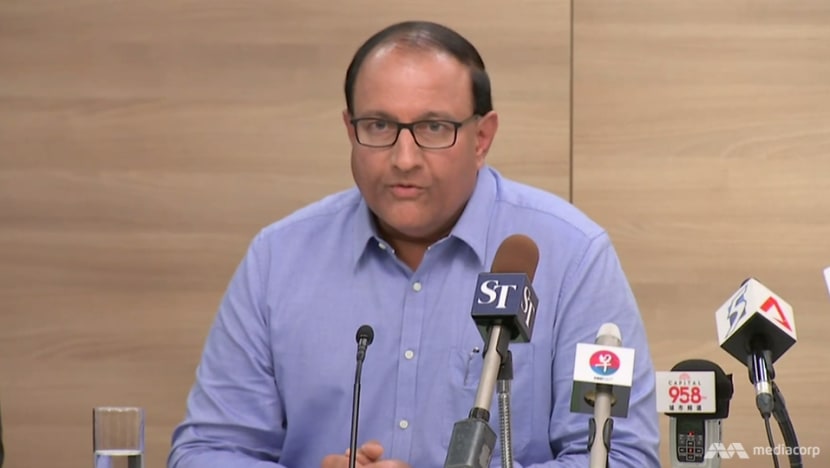
Minister for Communications and Information S Iswaran addresses reporters at a news conference on Friday (Jul 20) on the SingHealth data breach.
SINGAPORE: In the wake of the SingHealth data breach, it behoves both computer users and citizens to remember that cyberspace was originally intended to be the information superhighway for all. It was deliberately designed to be omnidirectional in communication.
Everyone who is on the Internet should ideally be able to reach everyone else. Underpinning this design for accessibility lay large assumptions about gentlemanly conduct, humaneness, and transparency in reciprocal contact.
As it has evolved, cyberspace also affords criminal elements a global presence.
Governments too, reacted understandably to impose "offline law" on cyberspace in the name of protecting their citizens from harm arising from the misuse of information. Theft of personal information, the stealing of identities, hate propaganda, financial fraud and abuse of others’ reputations quickly abounded as the darker side of the information superhighway.
In the course of policing against these harms, certain governments creatively inverted these malpractices as tools for cross-border penetration to pursue their respective national interests.
It is therefore no surprise that when Minister for Communications and Information, S Iswaran, declared that even though Singapore’s Cyber Security Agency (CSA) could identify the "Advanced Persistent Threat" group that hacked SingHealth, he could not publicly name the perpetrators.
TRIALS OF STRENGTH BY STEALTH
Insights from academics that study the security implications of cyberspace signal that anonymity, long distance penetration, remote control exercised through information technology, and above all, the quality of stealth add up to a new international order in cyberspace.
This order operates in parallel to what we understand of visible international relations conducted openly in full glare of the world’s press and social media.
In open diplomatic relations, even in overt military intervention, attribution and blame are visible and legally actionable. In cyberspace, the ability to extend communication globally overrides most legal restraints in daily use even if national rules are in place.
Moreover, as the US Defence Advanced Research Projects Agency has declared, the whole idea of the Internet was meant to be an infinitely replicable and survivable communications network.
Even China’s mighty censors have occasionally admitted that cyberattacks inside China cannot be completely prevented and foreign agencies can still attempt to hijack legitimate user addresses to penetrate China’s “sanitised” Internet.
As strategist Chris Demchak has argued, the cyber dimension of international order pits “wars of disruption” against “wars of resilience”.
In relation to the SingHealth incident, we can probably guard against a repeat of the last form of hacking with the benefit of hindsight but we have to be mentally prepared for newer, exotic forms of hack methods, by bouncing back to normality as quickly as possible.

SHOULD CYBER HACKERS BE NAMED?
The question of whether to name or not to name the cyber hackers revolves around one’s estimation of the severity of damage to national security and the reliability of cyber forensics in being 100 per cent confident in identifying the perpetrator.
The two issues may even overlap. During the suspected Russian-sponsored cyberattacks against Estonia in 2007, the damage had amounted to an assault on both the Estonian banking industry and its entire government.
The damage could even be assessed in millions of dollars. Yet the confirmation of Russian official culpability was never fool-proof.
Smaller airports in the UK and the US have also been systematically disrupted by viruses sent from abroad to mangle passenger booking software. North Korea too has only been heavily suspected of sanctioning disruptions of Sony’s Playstation and interference against South Korean banking operations.
In all of these cases, culpability could not be guaranteed to hold up in any court of law.
In the Middle East, several pairs of longstanding rival states have also taken to cyberspace to conduct tit-for-tat operations with little impact on the main offline political divides.

This slew of precedents suggests that the red line of "catastrophic damage" arising from a cyberattack remains mostly in the realm of intelligent projection, with the exception of Estonia’s experience in 2007.
Moreover, most sophisticated hackers have found ways and means to mask their complete identities such that even the best forensic teams will have to surmount a high threshold of proof before producing an indubitable charge.
RISKY TO NAME PERPETRATOR
To name a perpetrator in the absence of incontrovertible proof and catastrophic damage may risk upsetting existing diplomatic relations, sour the bilateral economic climate, or worse, initiate a conventional war which both sides do not want.
In the meantime, cyber hacking of the state-sponsored variety is here to stay.
For some it may be the ultimate form of power politics exercised in the shadows, displacing the confidence of a target population and its government, without direct political exposure.
For Singaporeans, the practical lesson is that digital hygiene is the shared responsibility of government, citizens and private sector.
Practical steps can mean changing personal passwords frequently and scanning access points for unusual patterns of activity. The solution cannot be simply a case of applying more information technology complexity to guard information technology.
Alan Chong is Associate Professor in the Centre of Multilateralism Studies, S Rajaratnam School of International Studies in Singapore.