commentary Business
Commentary: The way companies look to fend off cyberattacks needs a rethink
Companies whose operations are less digitally reliant tend to take a reactive stance towards cybersecurity, says one cybersecurity expert.
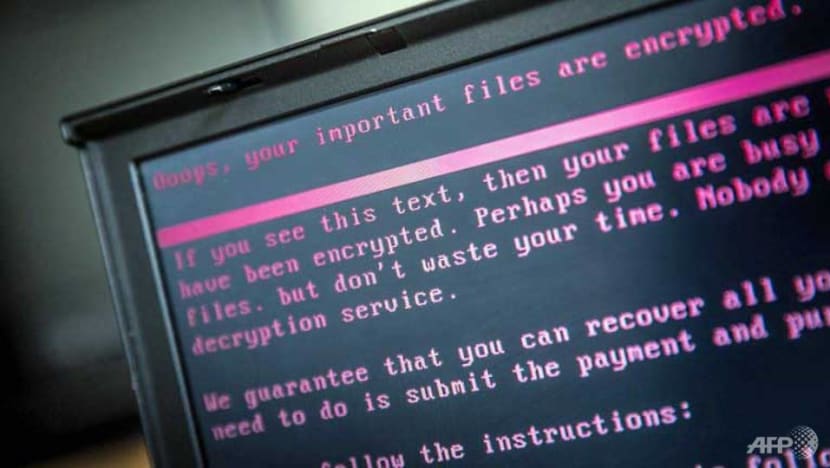
A laptop displays a message after being infected by a ransomware. (Rob Engelaar/ANP/AFP)
SINGAPORE: Companies are paying billions of dollars for fines and damages caused by cyberattacks. The number of breached records is skyrocketing and regulators around the world are tightening laws and penalising negligence, with minimal tolerance for laxity.
The most recent SingHealth hacking incident and last year’s attacks on NUS and NTU show that Singapore is just as vulnerable as other developed countries.
Cyberattacks and cybercrime are very real, and they happen every day.
We have observed that companies and organisations in Singapore whose operations rely heavily on digital forms of communications or payments are readily invested in cybersecurity capabilities with monitoring services and attack-detection capabilities.
However, other companies whose operations are less digitally reliant tend to take a reactive stance towards cybersecurity; remedial action is only taken after a breach, a significant close-call or if their competitor gets hacked and jailed.
This is where the danger lies.
Regardless of the nature of any business, the reality is that day-to-day communications today all take place online, making any organisation with any form of electronic communications susceptible to data breaches.
RETHINKING CYBERSECURITY
It is easy to assume that the management of cyber risks is the responsibility of the IT department, with the more sophisticated the system, the higher the level of security. But no technical solution will solve the current state of affairs.
CEOs should be held accountable when cybersecurity breaches happen: CSA chief
It has been found that more than 80 per cent of cyberattacks against organisations actually occur through targeted employees, often through phishing email attacks and the reuse of leaked passwords.
While most of us know by now not to click on links and files sent through suspicious-looking emails, the reality is that with an average of more than 90 accounts per Internet user, there is a high likelihood that one of these services are likely to be breached.
As a result, all the user passwords of that breached service become the entry point for hackers to access other systems. This is how most hacks begin. Whether or not that access leads directly to the organisation’s core system doesn’t matter as hackers are increasingly targeting social media profiles.
A hacker may, for example, log in to an employee’s LinkedIn profile and send a message with a link or attachment to someone else he is chatting with. Disguised as a message from a trusted party, that person opens the link and access is granted.
PASSWORD PROBLEMS
Sadly, many organisations today still practise sharing key account passwords within the team. This practice is often a catalyst for immediate security failure when those passwords are leaked.
For example, several people within the finance, accounting and database management divisions may share a common password for access to key files or accounts such as the company’s Twitter profile or the finance department’s email address.
The danger is that the use of leaked passwords will not trigger any alarms, as it’s generally seen as normal and legitimately successful login attempts.

In reality, having security measures such as the requirement to change passwords every 90 days can actually undermine, rather than bolster, the organisation’s best-laid plans to fend off attackers. Making frequent password changes a mandatory practice, and enforcing password-complexity requirements such as capital letters, numbers and special characters, kills creativity.
This tedious process also leads people to use simple passwords that are easy to remember - and predictably easy to decipher. Think passwords like “January2018!” and “P@ssw0rd”. There really is no need to change a password as long as the system has not been compromised and the password is unique.
When it comes to password protection, the only game-changer from the hacker’s perspective is in its length and uniqueness. Passwords with more than 25 characters that are unique rarely get reused and they also demand that users be innovative when creating them. When they are encrypted inside the solution, software or service, they will be the last ones to be cracked.
Password manager applications are a good solution too. But if you are concerned about their level of security, given that nearly all of them have been hacked, a poem or a shopping list would serve well as a password. It would do a better job in minimising the chances of being hacked than the typically-advised uppercase and special character tweaks.
COI for SingHealth cyberattack: IT gaps, staff missteps contributed to incident, says Solicitor-General
We have discovered from our research that more than 4.3 billion passwords to different online accounts worldwide have been breached over the past three years. That is one in every three accounts. So it is increasingly likely that your organisation’s information is also vulnerable. Re-assessing your organisation’s cyber resilience with password policies needs to be the first step to securing it.
AS SIMPLE AS 1, 2, 3
In my experience, successful companies put a lot of effort into understanding and simplifying things. It is not so much the outcome that matters, but the process.
Good cybersecurity starts with the identification of what comprises critical information for an organisation. The next step is to be able to identify where this information is located and how many people can access it.
While this may seem to be a very simple approach, it does require people within the organisation to have a shared understanding and agreement of what to protect and how to control access to the information. When everyone understands what they are protecting, user-awareness training can be designed to emphasise this and consequently, it becomes easier to motivate employees to follow practices and principles to safeguard it.
It’s impossible to secure everything, but you can certainly make critical information more secure.
There was this private wealth management firm seeking to boost its cyber resilience that I consulted for. It identified that its clients’ portfolios were the most critical information of value to them, but unfortunately, it was spread all around the organisation typically via email conversations.
For efficiency, these emails were accessible by employees on their smartphones, and, as you may have guessed, their phones are often used by spouses and kids, even friends.

In this case, simply disabling portfolio attachments in mobile devices to limit access to critical was sufficient as it didn’t affect productivity and these are typically handled at the office anyway.
If I boil it down, cybersecurity can and should be as easy as 1, 2, 3:
- Identifying your most critical information. What is the most critical information on which the survival of the company depends? What information could be used against you if a rival acquired it?
- Where is this information located? The answer is not a country, city or geographical area, nor is it a “secured server” or the cloud. What matters is where is it being copied. It is idealistic to think that all our critical information is safe in secure servers, but in fact it is probably most vulnerable in places where you can access it on the go. Is it on a desktop, laptop or mobile phone or outsourced to a third party? Is it in your emails that are downloadable on several devices? Or that USB stick that you left lying around in office.
- How many people have access to this information? It may sound impersonal, but it is best at first to simply think in terms of numbers. Once you come up with a number, you will be able to make decisions about whether it is a good number or whether too many people have access to the crown jewels of data.
These answers are the fundamentals of ensuring cyber resilience. With these in hand, enlisting the help of experts to secure what is critical within your organisation makes a lot more sense.
Mikko Niemelä is the CEO of Cyber Intelligence House, which specialises in the detection and monitoring of cyber exposure from the dark Web, deep Web and data breaches. He is also a lecturer at NUS Business School and Insead.















