No reports of Petya ransomware infection in Singapore, govt systems safe: CSA, GovTech
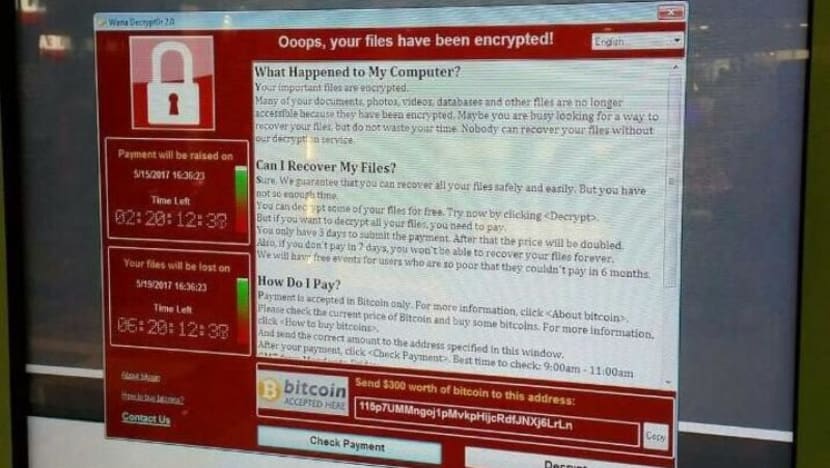
The Petya ransomware crippled computers running Microsoft's Windows system by encrypting hard drives and overwriting files, then demanded US$300 in bitcoin payments to restore access. AP File Photo
SINGAPORE — While no critical infrastructure or systems in Singapore have been affected by the Petya ransomware attack, the latest international cyber attack has left companies here scrambling to beef up their defences or take precautionary measures.
Experts have warned that Petya will inflict far more damage than the WannaCry virus, which caused unprecedented cyber disruption around the world in May.
In a joint statement on Wednesday (June 28) afternoon, the Cyber Security Agency (CSA) and Government Technology Agency (GovTech), said that SingCert (Singapore Computer Emergency Response Team) had not received any reports of Petya attacks.
"None of Singapore's 11 critical information infrastructure sectors were affected; our government systems have not been affected.
"GovTech has put in place a range of measures which minimises the likelihood of government systems being infected by malware, including ransomware," the statement added.
While no company has made reports to SingCert yet, global companies that have fallen victim to Petya and have offices in Singapore include shipping operator Maersk and marketing communications services group WPP, whose employees here were affected by Petya attack.
The ransomware attack - where a malicious malware essentially takes over a machine and prevents users from accessing data on the computer until a ransom is paid - is believed to have first struck Ukraine on Tuesday, before causing havoc around the world on Wednesday.
WPP has several companies in Singapore, including public relations companies Ogilvy Public Relations, and Burson-Marsteller.
Singapore employees of a company under WPP were scrambling to follow instructions, which came early Wednesday morning, on how to deal with Petya. They were told to log off from the office Wi-Fi network or servers, and make arrangements to work remotely.
Some worked from home using their personal computers, while other teams met in public spaces such as cafes, said an employee, who declined to be named as she was not cleared to speak to the media.
When asked to confirm if its Singapore entities were among those affected, a WPP spokesman would only say that "a number of WPP companies, though not all, were affected by the ransomware attack that hit organisations around the world".
"Our operations have not been uniformly affected, and issues are being addressed on a company-by-company basis. Many of our businesses are experiencing no or minimal disruption," said the spokesman.
Victims of the Petya attack would have seen their computers being rebooted, followed by a ransom note being displayed on their screen, asking for $300 in bitcoins to be paid, before they can recover their files.
However, even if victims pay the ransom, they are not likely to get their files back, said experts.
Mr Matthew Moynahan, chief executive officer of security software company Forcepoint, said: "There appears to be just one BitCoin wallet that is being used to collect the payments, but the support email address associated with the ransom demand has since been deactivated. It looks pointless to pay."
According to Internet security software company Kaspersky Lab, at least 2,000 organisations across the globe, including in Ukraine, Russia, United Kingdom and the United States, had been infected by the Petya ransomware.
However, compared to WannaCry, Petya seemed to be targeting enterprises rather than consumers.
Mr Moynahan noted that the ransomware had been designed to encrypt file extensions "typically found in an enterprise environment".
Mr Nick Savvides, security advocate, Symantec Asia Pacific and Japan, added: "Manufacturing organisations, which are highly concentrated in Asia, are particularly at risk as most do not apply updates and patches to their industrial computers as swiftly as corporate entities. This makes them especially vulnerable to rapid infections and complete shutdowns."
Meanwhile, some companies in Singapore are not taking any chances.
Food distribution company FoodXervices Inc, which had suffered two cyber attacks in the past year, is upgrading its enterprise resource planning (ERP) system. The move will include a crucial security aspect, such as a cloud-based backup of its systems.
"It means that we can still carry out our most critical operations, should we suffer an attack", said managing director Nichol Ng.
The WannaCry ransomware attack in May crippled computer systems in more than 100 countries. While no critical information infrastructure in Singapore were hit, reports said about 500 Internet Protocol (IP) addresses here could have been affected by the ransomware.












