What is the Pegasus spyware scandal and how is Singapore affected?
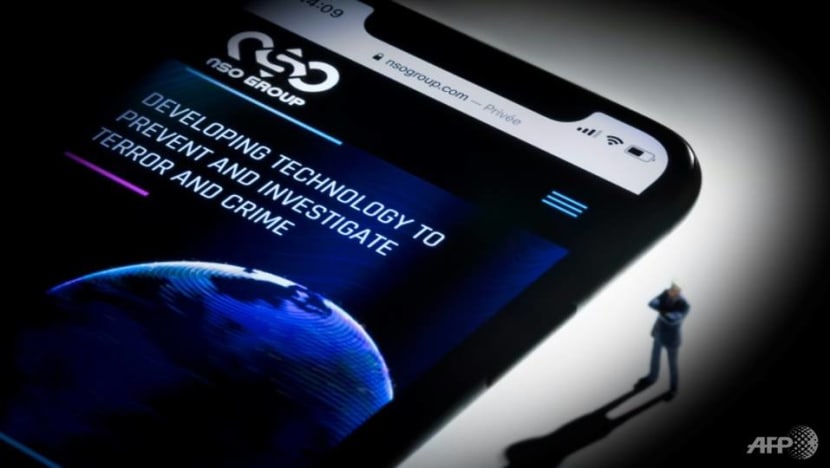
SINGAPORE: On Jul 18, major news outlets worldwide published an investigation into a massive data leak that showed rights activists, journalists and politicians around the world were targeted by authoritarian governments using hacking software sold by an Israeli surveillance company.
The company, NSO Group, produces Pegasus, a type of malware that infects iPhones and Android devices to enable operators of the tool to extract messages, photos and emails, record calls and secretly activate microphones.
The data leak contained more than 50,000 phone numbers suspected to be infected with Pegasus. They belong to hundreds of business executives, religious figures, academics, NGO employees, union officials and government officials, including ministers, presidents and prime ministers.
Notable individuals in this list include French President Emmanuel Macron, Financial Times editor Roula Khalaf and people close to slain Saudi dissident Jamal Khashoggi.
Prior to this, a Canada-based research group found in 2018 that some of the infected phones could be in Singapore.
However, the presence of a number in the recent leaked data does not mean there was an attempt to infect the phone. Without forensic examination, it is impossible to say whether the phones were attempted to be or successfully hacked using Pegasus.
The list of numbers was first obtained by Amnesty International, a human rights watchdog, and Forbidden Stories, a group that focuses on free speech. They then shared the list with a consortium comprising journalists from 17 prominent news outlets.
The consortium's analysis of the leaked data identified at least 10 governments believed to be NSO customers who were entering numbers into Pegasus, according to a Jul 18 report by the Guardian, which is part of the consortium.
The governments include that of Azerbaijan, Bahrain, Kazakhstan, Mexico, Morocco, Rwanda, Saudi Araba, Hungary, India and the United Arab Emirates.
Rwanda, Morocco, India and Hungary have denied using Pegasus to hack the phones of individuals named in the list, while the rest did not respond to requests for comment, the Guardian report said.
Related:
NSO has rejected the claims arising from the data leak, but said it would "continue to investigate all credible claims of misuse and take appropriate action".
The company insisted that Pegasus is only intended for use against criminals and terrorists, and that it only sells to military, law enforcement and intelligence agencies in 40 unnamed countries. These customers have been vetted for their human rights records, NSO said.
But it is not difficult for bad actors to create legitimate-looking shell companies and deceive sellers of such sensitive tools, said Mr Vitaly Kamluk, director of the global research and analysis team (APAC) at Kaspersky.
"It's possible to create someone who will just represent you and look like a legal entity that may be connected to the government," he told CNA on Wednesday (Sep 22).
"Some proofs can even be faked and I'm sure that if you really focus on this, you can find one way or another to become a legitimate customer of the NSO Group. And if you have enough money, you can buy these tools they offer."
NSO has attracted scrutiny since 2016, when the company's software was said to be used against a rights activist in the United Arab Emirates and a journalist in Mexico, the New York Times reported on Jul 18.
In 2018, an investigation conducted by University of Toronto research group Citizen Lab found that some of the phones suspected to be infected were in the UK, US and Singapore. Citizen Lab had also reviewed the work done by Amnesty researchers on the recent data leak.
The Singapore Government said on Sep 13 it is aware of these claims but cannot verify them as no reports have been filed.
"As our findings are based on country-level geolocation of DNS servers, factors such as VPNs and satellite Internet teleport locations can introduce inaccuracies," the Citizen Lab report said.
Because Singapore hosts a number of data centres and is a regional Internet communication hub, Mr Kamluk said, the findings could have pointed to Singapore's Internet infrastructure instead of actual victims living here.
Here's what we know about Pegasus so far:
HOW DOES PEGASUS INFECT A PHONE?
While earlier versions of the software used targeted spear-phishing attacks to gain access to a phone, it has since been made far more efficient, and is able to infect a device even if nothing is clicked on.
Mr Kamluk said Pegasus infects phones through "non-interaction" methods, which means malicious code is sent to a target and breaches the target's device "without any kind of user interactions required".
For instance, Pegasus first creates a fake WhatsApp account, then uses it to make video calls. When an unsuspecting user's phone rings, a malicious code is transmitted that installs the spyware on the phone. The software is installed even if the call is not answered.
Pegasus has apparently begun exploiting vulnerabilities in Apple's iMessage software as well, although Apple on Sep 13 released a fix to rectify this.
Still, Mr Kamluk said Pegasus will likely find new ways to continue exploiting iPhones through other backdoors.
"These vulnerabilities, they (Apple engineers) don't plant them on purpose, for sure, but it's in the fundamental code of our human nature to make mistakes," he said. "We will see new ones come and appear, and Apple will patch again the moment they find this."
When Pegasus is installed on a phone, it could gain administrative privileges on a device, allowing it to do even more things than the device owner.
"It's fully automatic," Mr Kamluk said. "They choose the target and at that moment the operator has full control of the device."
CAN PEGASUS BE IDENTIFIED AND REMOVED?
When Pegasus infects a phone, it hides itself but leaves some traces that can be spotted using specialised software, like the mobile verification toolkit published open source and free by Amnesty, Mr Kamluk said.
But to thoroughly check an iPhone, for instance, users would probably void their warranty as specialists would need to "jailbreak" the phone to check every single thing stored inside, Mr Kamluk continued.
"Of course, NSO Group will improve," he said. "So, everything that is detected right now – all these signs and traces that were picked up by Amnesty International and Citizen Lab – will be changed so that this tool will be blind to future versions of diagnosis (software)."
And because Pegasus burrows deep into parts of a device that require the highest privileges to access, Mr Kamluk said removing it will not be easy as uninstalling an app or stopping a service.
"If the phone is infected, that likely means that it will remain there for a long time. Depending on the exploits they have and the post-exploitation stages, it may actually get deeper and even survive the reboot or total reset of the (phone)," he added.
"Once the phone is breached, I would not recommend to use it to anyone who cares about privacy or security."
WHO ELSE HAS BEEN TARGETED?
Numbers on the leaked list include Mexican reporter Cecilio Pineda Birto, who was gunned down on the street, as well as journalists from CNN, the Associated Press, the Wall Street Journal, Bloomberg News and the New York Times.
Two of the targeted phones were owned by Mr Szabolcs Panyi and Mr Andras Szabo, investigative reporters in Hungary who regularly cover government corruption.
Indian investigative news website the Wire also reported that 300 mobile phone numbers used in India, including those of government ministers, opposition politicians, journalists, scientists and rights activists, were on the list.
WHAT ARE THE IMPLICATIONS?
The Pegasus leak is likely to spur debates over government surveillance in several countries suspected of using the technology.
The investigation suggests the Hungarian government of Viktor Orbán appears to have deployed NSO’s technology as part of his so-called war on the media, targeting investigative journalists in the country as well as the close circle of one of Hungary’s few independent media executives, the Guardian report said.
Related:
Without access to surveillance-free communications, journalists will no longer be able to contact sources without fear of exposing them to government retaliation. Rights campaigners will also be unable to freely communicate with victims of state-led abuses, the New York Times reported.
On Sep 15, the European Union justice commissioner said the bloc must swiftly legislate to further protect the rights of activists, journalists and politicians following the Pegasus spyware scandal.
Perpetrators of illegal tapping must also be prosecuted, Mr Didier Reynders told the European parliament.
Mr Kamluk believes the fallout will definitely lead to tougher regulations and control on what the NSO Group does and who it sells to.
"Right now, I think their reputation is damaged so badly that they will probably lose existing customers, and new customers are unlikely to appear anytime soon," he said. "If they survive, they will be strictly controlled."
HOW IS SINGAPORE AFFECTED?
On Sep 13, MP Leon Perera (WP-Aljunied) asked if Singapore would investigate the Pegasus findings and identify the operators behind the suspected infection of mobile devices in Singapore.
In response, Minister for Communications and Information Josephine Teo said the Government is aware of open source claims of potential Singaporean victims of Pegasus dating from 2018, but that these claims cannot be verified as no report has been filed.
Members of the public who suspect that their mobile device has been infected with spyware, including Pegasus, are advised to lodge a police report or report the incident to the Singapore Computer Emergency Response Team, she said in a written reply.
"The threat of electronic surveillance by hostile actors is not new. Our security agencies continually invest resources to guard against such threats to our systems," she added.
"At the individual level, to mitigate the risk of spyware and other malware, we should also adopt good cyber hygiene practices, such as avoiding untrustworthy websites and not opening suspicious attachments."
Mr Perera did not respond to requests for comment.
Mr Kamluk said Citizen Lab has in the last few years reported on digital attacks on civil society, and has been a "quite consistent and credible source".
"I would say they do quite a professional job, and they are good at this. So, I don't see any reasons not to believe what they shared with the rest of the world," he said.
Still, the director of Kaspersky's global research and analysis team Costin Raui said Citizen Lab's methodology primarily identifies the location of Pegasus command and control servers, not victims.
"In principle, this methodology provides an approximate victimology, which may or may not be identical to the true location of the victims. Unfortunately, we have no visibility or direct knowledge of any victims they may have identified in Singapore," he told CNA.
Mr Kamluk said governments around the world should take the potential threats of Pegasus seriously.
"I think it has to be solidly investigated, because we're seeing zero-click non-interaction exploits. Now, a prime minister or members of parliament can be targeted," he said.
"So, all (attackers) need to know is their personal Apple ID or phone number in order to attack them and then to get probably classified confidential information right from their devices, be it eavesdropping on the sound, the camera, documents, emails and access to other potential work-related accounts from those devices.
"It's not just a yet another story, but it is a serious, serious case."














